Using Analytics to Improve Customer Engagement
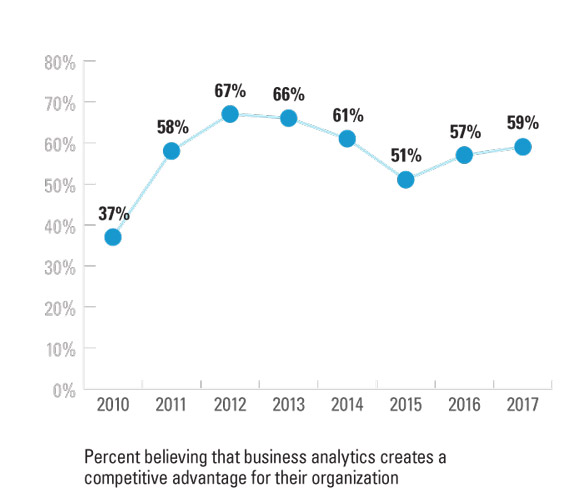
Here is a guest blog from MIT SMR by Sam Ransbotham. Organizations that turn data into insights are gaining competitive advantage through improved connections with consumers.… Read More »Using Analytics to Improve Customer Engagement